In the previous articles we have discussed about the various types of attacks that can happen on an IoT device. In this article, we will discuss about the security measures laid out by the OWASP (Open Web Application Security Project ). The OWASP top 10 IoT vulnerabilities list is a resource for manufacturers, enterprises, and consumers. Its goal is to help organizations and individuals gauge the acceptable risk and make an informed decision about releasing or purchasing a product. The security measures are as follows,
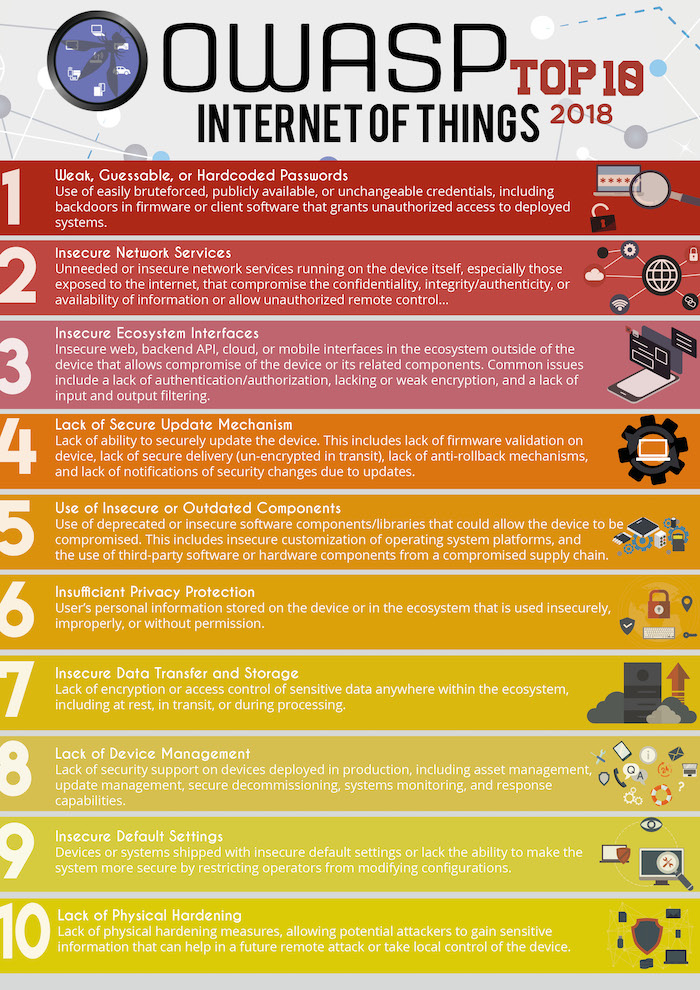 1. Weak, Guessable, or Hardcoded Passwords
1. Weak, Guessable, or Hardcoded Passwords
In most of the IoT devices, users are not allowed to change the password. Once programmed the password cant be reconfigured. A hacker could easily use brute force to crack the password. This allows the device to be a host vulnerable for multiple attacks.
- Depending on the sensitivity of the information being protected, change passwords periodically, and avoid reusing a password for at least one year.
- Do use at least eight characters of lowercase and uppercase letters, numbers, and symbols in password.
2. Insecure Network Services
When the ports are left the device security can be compromised and susceptible to DDoS attacks. If left long enough, the network will be a part of botnet. The following steps will be useful in minimizing the attacks
- Ensure the inward and outward ports are monitored. Use Nmap to list all the open ports and close them if necessary.
- Use IP filter to limit the access to limited persons.
- Disable any services that provide remote access
- Keep your system updated
- Never connect your device in a public network.
3. Insecure Ecosystem Interfaces
Interfaces like the web, cloud, mobile, or back-end API that allow users to interact with the smart device can have vulnerabilities in the implementation of authentication/authorization, weaknesses in encryption, data filtering, etc. These security flaws can eventually lead to compromising the device or any of its related components.
4. Lack of Secure Update Mechanisms
The concern here is that many IoT devices lack the ability to securely update. Update mechanisms should also support
- Anti-rollback mechanisms
- Secure delivery (not sending the update in cleartext, signing the update, etc.)
- Firmware validation on the device.
5. Use of Insecure or Outdated Components
Using outdated software or insecure libraries in code could lead to compromising the overall security of the product. From insecure customizations of the operating system to using vulnerable third-party hardware or software components, IoT vulnerabilities include anything that injects weaknesses into the device can be used as an entry point or leveraged to perpetuate an attack.
6. Insufficient Privacy Protection
Over collection and over retention of user data, especially now that IoT is such a huge part of peoples everyday lives, can also lead to compromising their security in the physical world.
7. Insecure Data Transfer and Storage
In addition to restricting access to sensitive data in general, it’s crucial to ensure that data is encrypted when at rest, in transit, or in processing. If encryption is not strictly implemented, it leaves data vulnerable and becomes a major IoT security concern if it’s missing from smart devices.
8. Lack of Device Management
It is critical to know what assets are on network and it’s also equally important to manage them efficiently. Regardless of the size of the devices or their individual costs, if they’re interacting with the network and have access to it, then managing them methodically should be one of primary concerns.
9. Insecure Default Settings
The default passwords or device configurations on smart devices are often insecure. While sometimes it is just negligence on our part that we do not change default settings, at other times, it is not possible to alter system settings like hardcoded passwords, exposed services running with root permissions, etc.
10. Lack of Physical Hardening
Hardening the device against physical attacks protects it against attempts by malicious users to extract sensitive information that can later be leveraged to launch a remote hack or gain control of the device. For instance,
- Debug ports that are usually not removed or disabled leave your devices vulnerable to access by hackers.
- Using secure boot helps validate firmware and ensures that only trusted software can run on the device.
