Cyber attacks on IoT devices
VoLTE encrypts call data as it passes between a phone and a base station. The base station then decrypts the traffic to allow it to be passed to any circuit-switched portion of a cellular network. The base station on the other end will then encrypt the call as it’s transmitted to the other party.
The implementation error ReVoLTE exploits is the tendency for base stations to use some of the same cryptographic material to encrypt two or more calls when they’re made in close succession. The attack seizes on this error by capturing the encrypted radio traffic of a target’s call, which the researchers call the target or first call. When the first call ends, the attacker quickly initiates what the researchers call a keystream call with the target and simultaneously sniffs the encrypted traffic and records the unencrypted sound, commonly known as plaintext.
Man in the Middle Attack
The man-in-the-middle concept is where an attacker attacks during IoT routing. Man-in-the-middle is a type of eavesdropping attack that occurs when a malicious actor inserts himself as a relay/proxy into a communication session between people or systems. A MITM attack exploits the real-time processing of transactions, conversations or transfer of other data.
 Neuralink
Neuralink  Cyber Security
Cyber Security  Ngrok
Ngrok 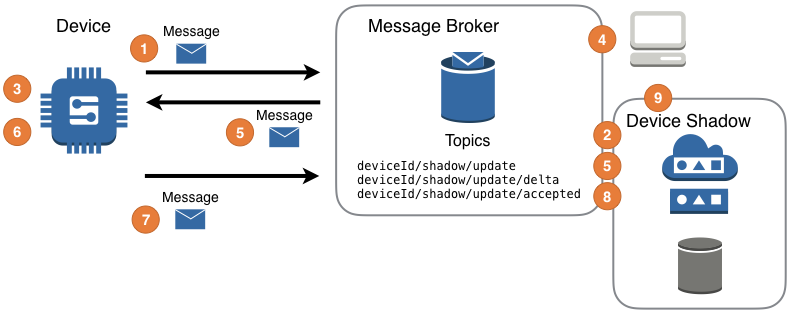 Exploring AWS IoT Device Shadow
Exploring AWS IoT Device Shadow